28 May 2025
How We Eliminated Proxy Attendance in Gujarat’s Schools
Access Computech introduced fingerprint-based biometric systems across Gujarat’s schools to stop proxy attendance and ensure accurate, tamper-proof records.

28 May 2025
Access Computech introduced fingerprint-based biometric systems across Gujarat’s schools to stop proxy attendance and ensure accurate, tamper-proof records.

Manual register-based attendance is still widely used. However, it has many flaws, despite its worldwide acceptance. But the one flaw that has the potential to discredit the entire system is proxy attendance. Whether it be the student's attendance or the staff’s.
In manual methods, proxying is very easy to do, even harder to detect, and almost impossible to challenge.
A student’s friend could mark them present. A teacher could just fill out the entire list at the end of the week. Or a staff member could misuse it to mark working days despite being away from work. A few numbers change, and it’s nearly impossible to prove what really happened.
It’s not that the system was broken because people weren’t working. The real problem was that there was no way to know if what was on paper matched what happened in real life.
So that’s what we had set out to fix. Not with the intention of any suspicion or surveillance, but with a simple idea to let the system verify itself.
Our solution reduced a lot of admin workload, divided responsibility on crucial processes such as attendance marking, and automated the monitoring and analysis of attendance trends and patterns in the state’s schools.
Across Gujarat’s government schools, attendance was still being recorded by hand. This meant:
The bigger problem? These records were the foundation for decision-making. This data was used to evaluate performance reviews and for resource allocation. Student interventions and policies were set based on this data. And yet, the system was almost entirely dependent on unverifiable human memory.
We needed to shift the idea of attendance from being an assumption to being a fact.
We replaced manual registers with a biometric fingerprint-based system. This one change made attendance irrefutable.
At the core of the solution was a principle: you can only mark your attendance if you’re physically present, and only if the system confirms it’s you.
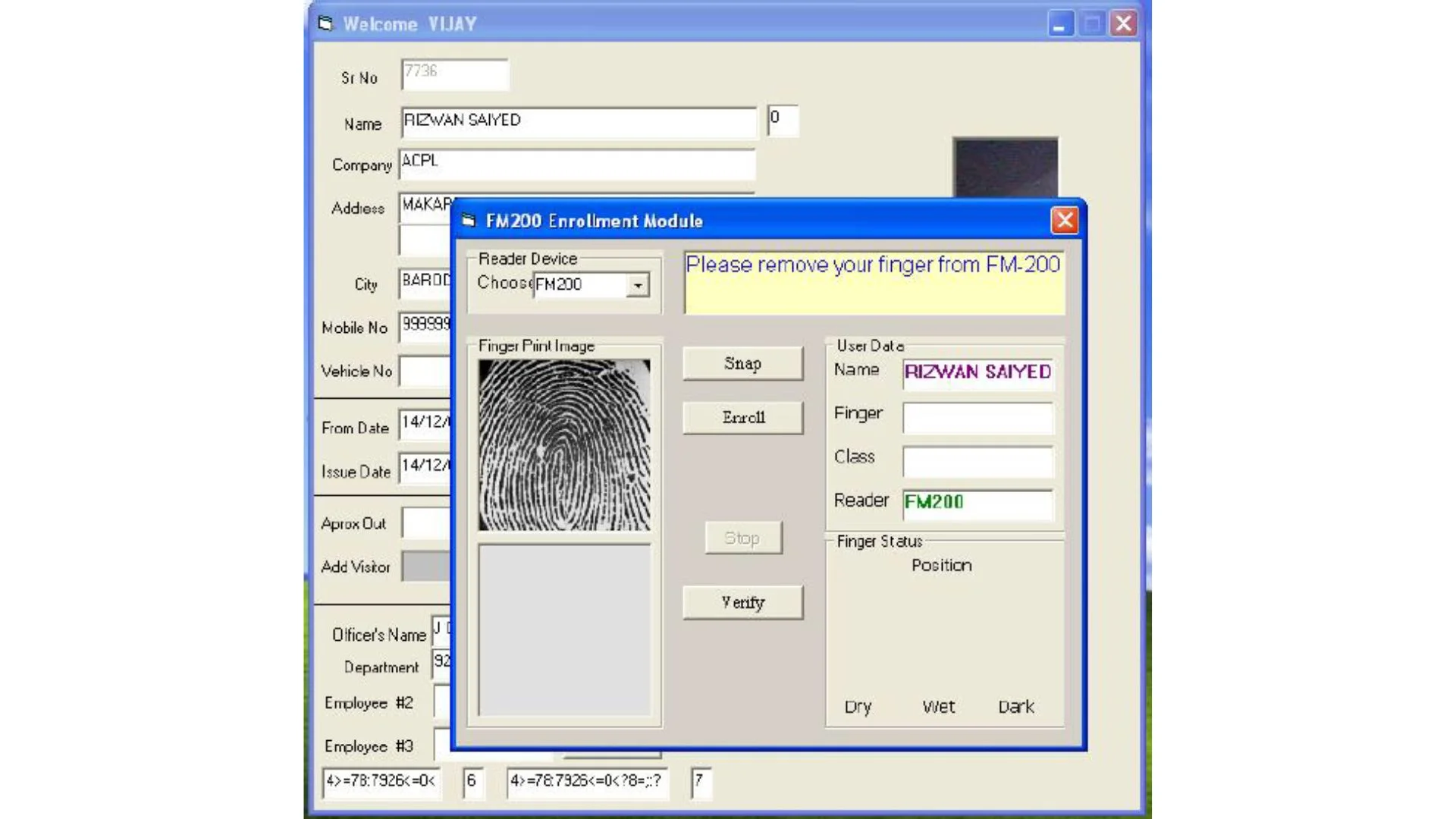
Every student and teacher was enrolled in the system with their fingerprint, captured and stored securely at the school level.
When they arrived each day, they simply scanned their registered finger at a device connected to the school’s system. The match had to be exact, or the entry wouldn’t register.
What this meant:
Of course, fingerprint-based systems are susceptible to manipulation as well. But we had a contingency ready, our devices are programmed to detect manipulation too.
Our system was designed to recognise fake fingerprints, duplicates, and suspicious patterns using multiple techniques:
This was a smart, layered verification system designed to keep the process honest.
As soon as attendance was marked, the data was recorded in real time and timestamped.
Every entry was secured, stored locally, and synced with district and state servers for central visibility.
There was no going back and changing things quietly. The moment was captured as it happened, and that became the record.
For regions with low or bad network connectivity, the data was stored locally and transmitted upon detection of a stable network in batches.
Or in cases where stable connectivity did not exist at all, the local data was transported to the district HQ and cross-verified to ensure it’s authenticity.
For the first time, school attendance became something you could trust completely.
Teachers could no longer be held responsible for manually chasing records or verifying student presence.
District officers didn’t have to wait a month to know if attendance was slipping.
And students? They knew the system couldn’t be gamed. They had to show up to be counted.
The impact was clear as day.
Attendance started going up because the system didn’t discriminate anymore. Patterns started to emerge, which will help the government create and implement relevant education policies for years to come.
Sometimes, fixing a problem isn’t about catching people, it’s about removing the opportunity for the problem to happen in the first place.
Proxy attendance was much more than a technical flaw. It was a gap in trust, accountability, and clarity.
By putting identity verification at the centre of the system, we completely eliminated fake entries and made every single attendance count. And that, in turn, made the whole system stronger.
At Access Computech, we’ve been delivering dependable, customised solutions for over 30 years, specialising in Point-of-Sale Machines and Personalised Identification Systems. From Attendance Recording and Access Control to Visitor Management, we create tailored systems that fit our clients’ unique needs.
Our tailored systems have enhanced efficiency across industries such as petrochemicals, refineries, steel, mining, power, electronics, and textiles.
With a passionate team and offices across the country, we stay ahead of the curve by adopting emerging technologies to deliver the latest, most reliable, high-quality solutions for our clients.
Our mission is simple: To consistently meet and exceed the expectations of our clients by adhering to the highest industry standards.
Our Certifications & Accreditations: Certified for excellence with ISO 9001, ISO 14000, ISO 27001, and CMM Level 3, we uphold industry-leading standards in every aspect of our business.